PV204 Security technologies Rootkits, reverse engineering of binary applications, whitebox model Petr Švenda Faculty. - ppt download
PV204 Security technologies File and disk encryption Milan Brož Petr Švenda Faculty of Informatics, Masaryk University. - ppt download

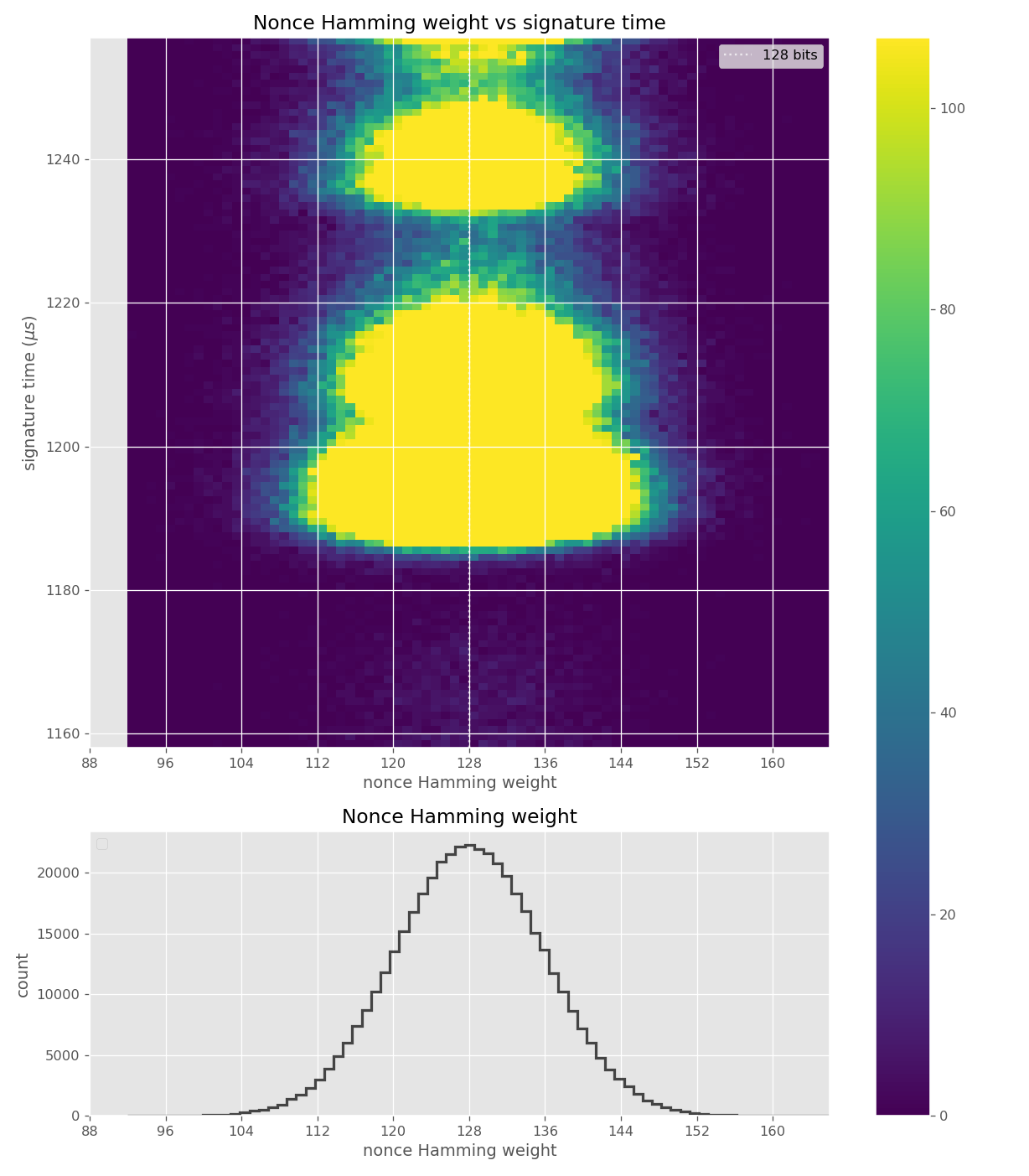
PV204 Security technologies Trusted element, side channels attacks Petr Švenda Faculty of Informatics, Masaryk University. - ppt download

![Research: Analysis of Trusted Platform Module chips [CRoCS wiki] Research: Analysis of Trusted Platform Module chips [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/tpm_bootmenu_1280.jpg)
![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/error-usability.png)
![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/jcalgtest_logo.png)
![ROCA: Vulnerable RSA generation (CVE-2017-15361) [CRoCS wiki] ROCA: Vulnerable RSA generation (CVE-2017-15361) [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/papers/roca_impact.png?w=400&tok=973b60)




![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/std.png?w=200&tok=2a296f)
![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/wsn.png)
![Research: Analysis of Trusted Platform Module chips [CRoCS wiki] Research: Analysis of Trusted Platform Module chips [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/tpm_info_1280.jpg)
![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/crocs/svenda.jpg?w=50&tok=2d8fb9)
![Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki] Research themes in CRoCS laboratory [crcs.cz/projects] [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/cards.png)

![Research: Analysis of Trusted Platform Module chips [CRoCS wiki] Research: Analysis of Trusted Platform Module chips [CRoCS wiki]](https://crocs.fi.muni.cz/_media/public/research/tpm_upload.png)

