CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
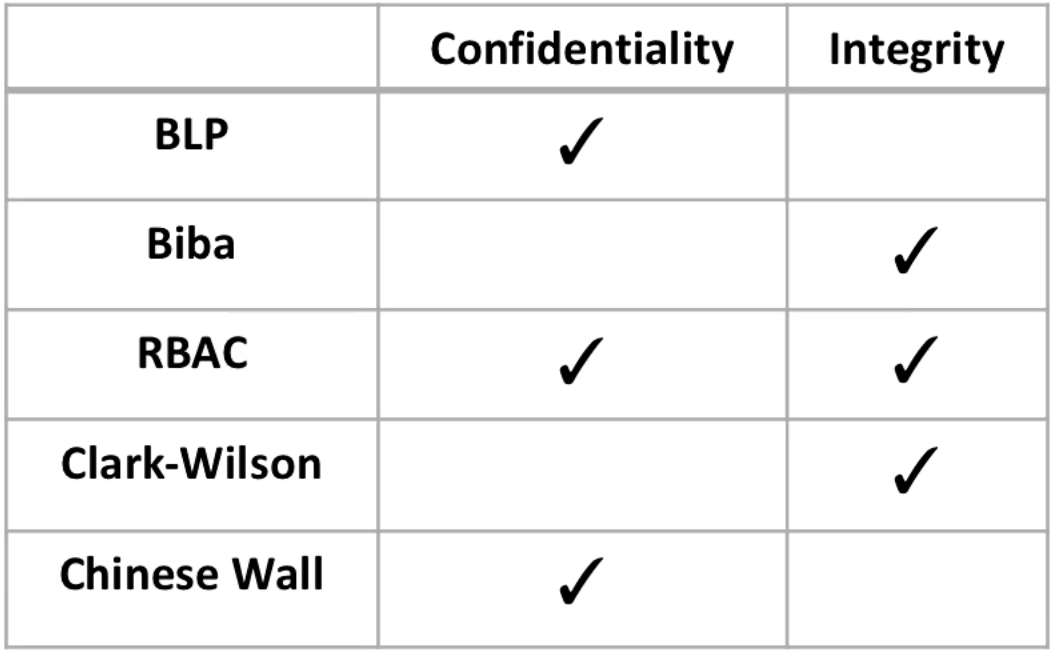
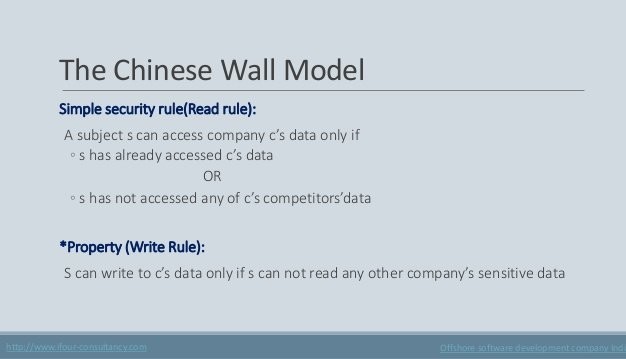
▻ Bell-LaPadula model ▻ Biba model ▻ Chinese Wall model ▻ (Clark-Wilson model) ▻ Demonstrate how security policies can

Session 2 - Security Models and Architecture. 2 Overview Basic concepts The Models –Bell-LaPadula (BLP) –Biba –Clark-Wilson –Chinese Wall Systems Evaluation. - ppt download
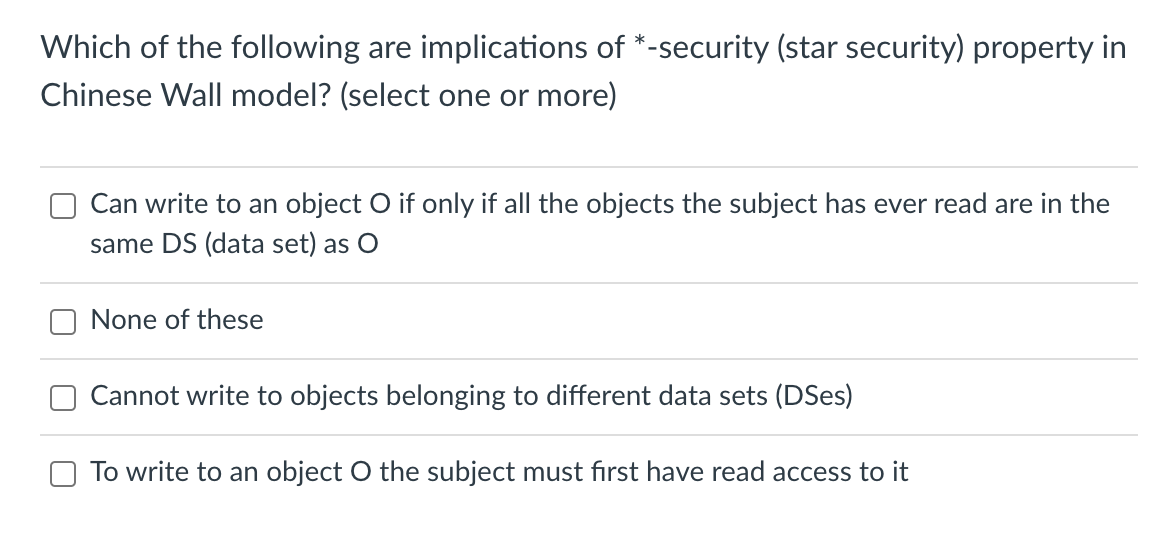
Integrity Protection: Biba, Clark-Wilson, and Chinese Wall | CS 42600 | Study notes Computer Science | Docsity

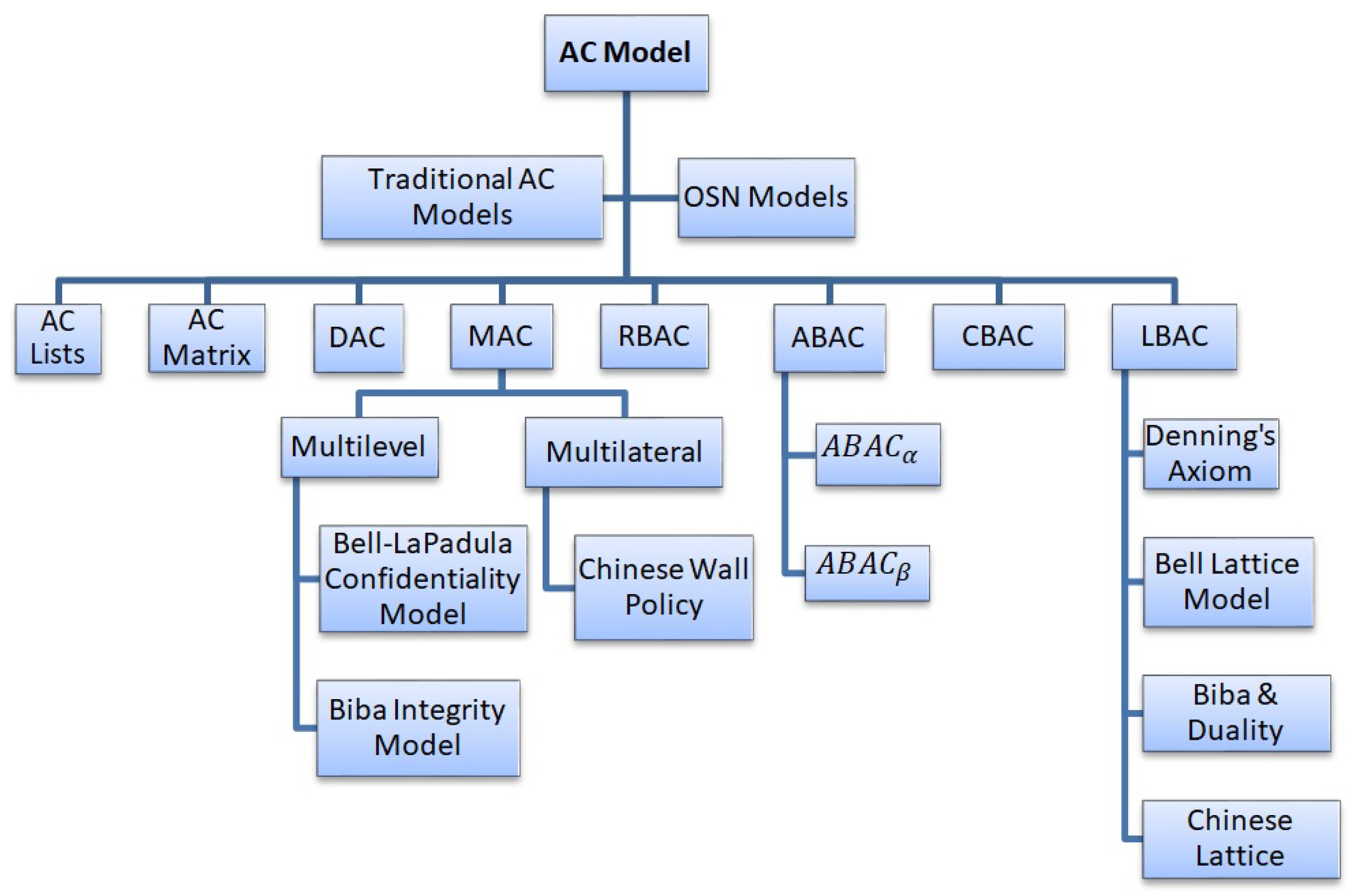
Generic metamodels for expressing configurations of (a) DAC; (b) BLP... | Download Scientific Diagram

Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu