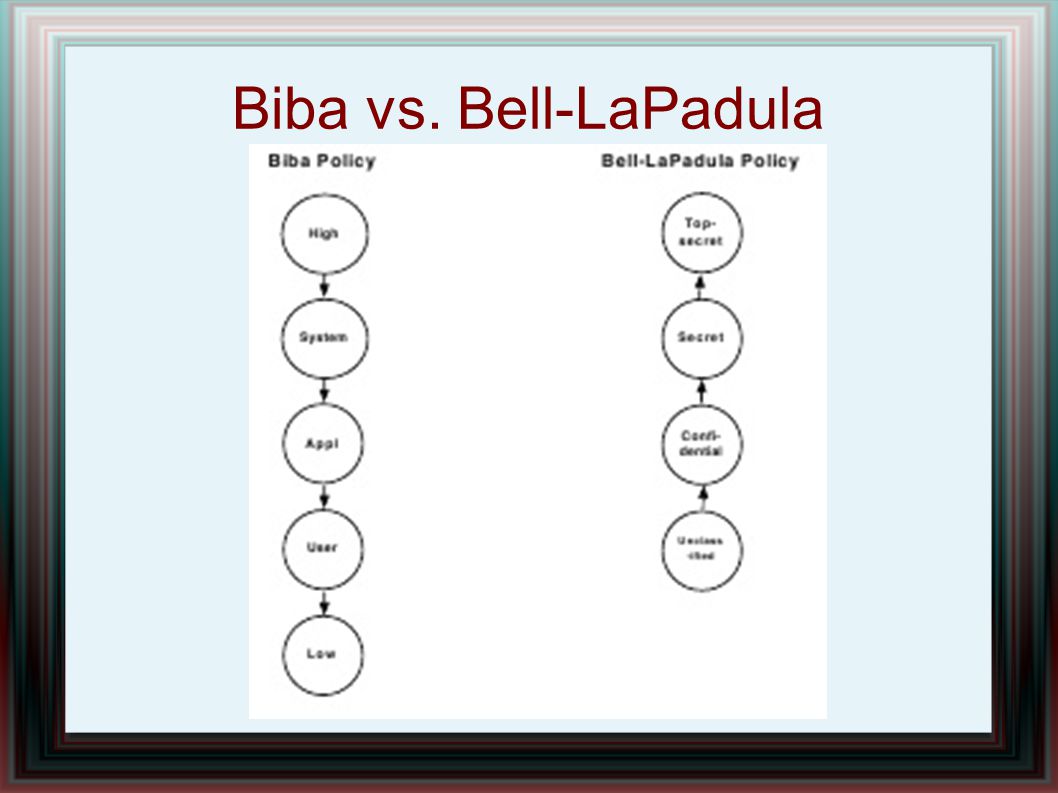
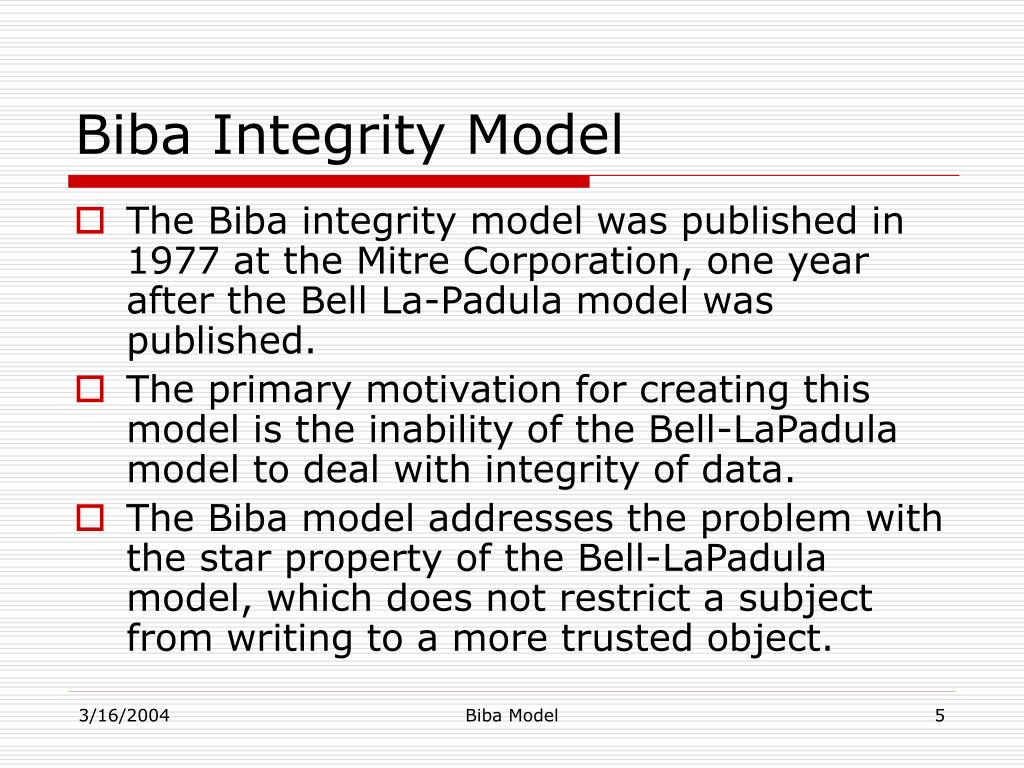
An Introduction to Multi-level Security Confidentiality: Clark-Wilson and Brewer Nash Models vs Bell-Lapadula and Biba Models – Umar's Blog
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S

CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu