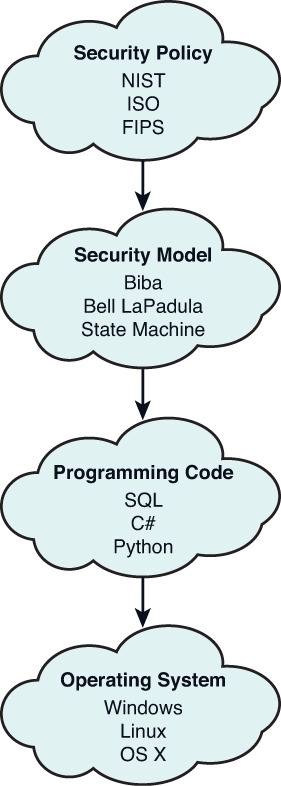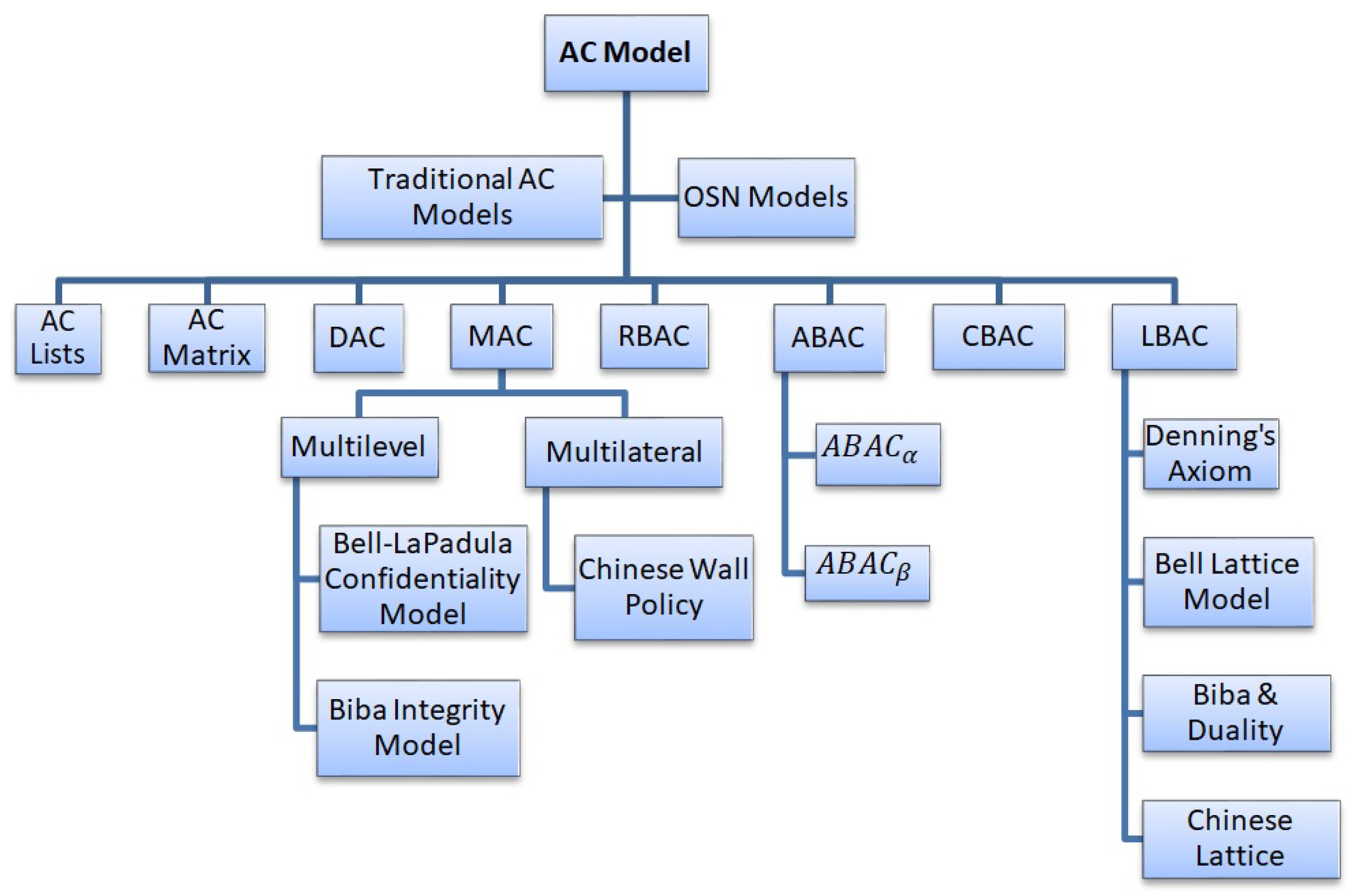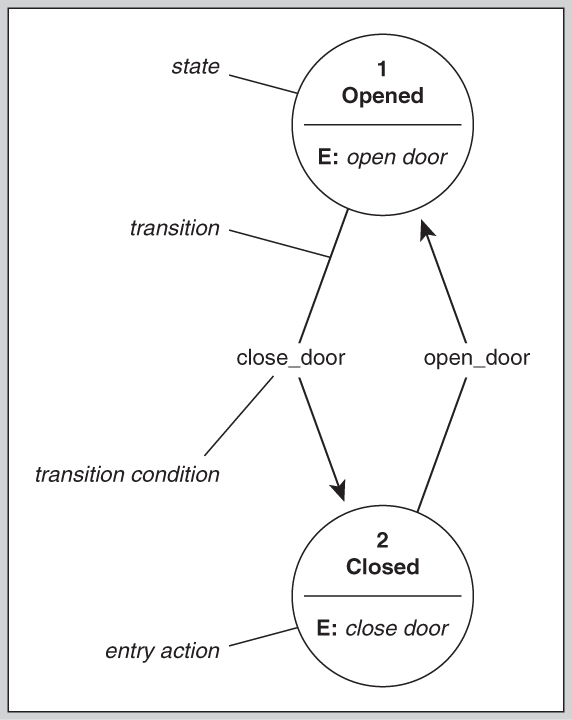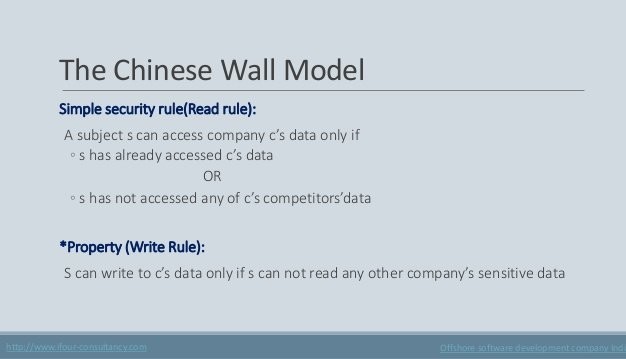
Session 2 - Security Models and Architecture. 2 Overview Basic concepts The Models –Bell-LaPadula (BLP) –Biba –Clark-Wilson –Chinese Wall Systems Evaluation. - ppt download
▻ Bell-LaPadula model ▻ Biba model ▻ Chinese Wall model ▻ (Clark-Wilson model) ▻ Demonstrate how security policies can

Which of the following models describe how subjects and objects must be created and deleted? - Skillset

An Introduction to Multi-level Security Confidentiality: Clark-Wilson and Brewer Nash Models vs Bell-Lapadula and Biba Models – Umar's Blog
CS361: Introduction to Computer Security Meaning of Computer Security Confidentility Ain't Enough Commercial Security

Security Models Pt 3 Clark-Wilson, Brewer and Nash, Graham-Denning (CISSP Free by Skillset.com) - YouTube

CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

What are the 5 Major Types of Classic Security Models? - Cyber Security Certifications, Cyber Security Consulting, RogueLogics

Managing Information Confidentiality Using the Chinese Wall Model to Reduce Fraud in Government Tenders | Semantic Scholar